With the deployment of enterprise workloads in multiple regions and cloud providers, legacy mesh networks are becoming costly, hard to implement, scale, and manage. Attempts by legacy vendors to adapt antiquated, castle-and-moat VPN and firewall architectures to the public cloud have allowed an unprecedented number of cybersecurity attacks, in addition to networking and application performance challenges for enterprises. As a result, organizations must rethink their approach to securing and connecting cloud-based applications and consider adopting new architecture able to simplify multi-cloud connectivity, elevate application performance, and provide comprehensive protection. Recent findings from the Zscaler ThreatLabZ research team underscore these challenges and outline the growing threat from unsecured workloads in the cloud and the need for inspection of all content including encrypted traffic.
To meet these needs,
Today’s general availability of
Application-to-Internet Communications – Cloud Applications require access to the internet for a variety of reasons, from communicating with third-party Application Programming Interface (API) services to receiving software updates. Using the Zero Trust Exchange, internet access is secured with ZIA policies that now include DLP and threat prevention while making workloads completely invisible to potential cyberthreats.Multi-Cloud Application-to-Application Communications - Multi-cloud networking allows organizations to secure connectivity across heterogeneous cloud environments. ZPA policies secure workload communications across cloud providers, regions, and virtual private clouds (VPCs) in the same public cloud for seamless and secure application communication without the complexities and performance bottlenecks that legacy technologies create.Intra-Cloud Application-to-Application Communications – To enable secure workload-to-workload communications inside a cloud, VPC/VNet , or data center,Zscaler uses a combination of macro and micro-segmentation to verify software identity. This includes microsegmentation of business-critical environments to prevent unauthorized communication between applications.
“To properly secure cloud workloads, three critical areas – security, connectivity, and performance – need to be addressed, which legacy approaches have not been able to solve,” said
Customer and Partner Quotes:
"As we move more applications to the public cloud, we must ensure a high level of compliance with internal and external requirements, avoid security risks from inconsistently applied controls, and reduce legacy infrastructure costs," said Rui Cabeço,
“While we share the responsibility of cloud security with our enterprise customers, we are customer obsessed in helping our customers accelerate secure workload migration to AWS to achieve scalability and agility,” said
About
Zscaler™ and the other trademarks listed at https://www.zscaler.com/legal/trademarks are either (i) registered trademarks or service marks or (ii) trademarks or service marks of
Media Relations Contact:
press@zscaler.com
A photo accompanying this announcement is available at https://www.globenewswire.com/NewsRoom/AttachmentNg/5abb33a2-92f0-4f2f-a512-e5fc04445084


Zero Trust Workload Communication
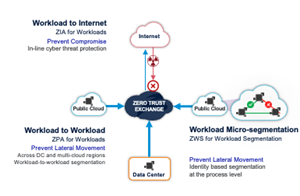
Zscaler’s new Workload Communications solution, part of the Zscaler Zero Trust Exchange, extends Zero Trust security to workloads and applications hosted in public clouds. Zscaler’s cloud-native platform eliminates attack surfaces, prevents lateral threat movement, inhibits compromise of workloads, and stops data loss. It also helps IT teams simplify multi-cloud workload connectivity by moving away from traditional IP-based routing and VPNs between cloud environments to expedite enterprises' cloud transformation initiatives.
2021 GlobeNewswire, Inc., source



