Yahoo was the most impersonated brand for phishing attacks during Q4 2022, climbing 23 places and accounting for 20% of all attempts.
In general, the technology sector was the industry most likely to be imitated by brand phishing in the last quarter of 2022, followed by shipping and social networks. DHL came in second place with 16% of all brand phishing attempts, ahead of Microsoft in the third spot with 11%. LinkedIn also returned to the list this quarter, reaching fifth place with 5.7%. DHL’s popularity could be due to the busy online shopping season surrounding Black Friday and Cyber Monday, with hackers using the brand to generate ‘fake’ deliveries notifications.
Top 10 Most Imitated Brands
Below are the top brands ranked by their overall appearance in brand phishing attempts:
- Yahoo (20%)
- DHL (16%)
- Microsoft (11%)
- Google (5.8%)
- LinkedIn (5.7%)
- WeTransfer (5.3%)
- Netflix (4.4%)
- FedEx (2.5%)
- HSBC (2.3%)
WhatsApp (2.2%)
Instagram Phishing Email – Account Theft Example
CPR observed a malicious phishing email campaign that was sent from “badge@mail-ig[.]com”. The email was sent with the subject “blue badge form”, and the content tried to persuade the victim to click on a malicious link claiming that the victim’s Instagram account had been reviewed by the Facebook team (the owner of the Instagram brand) and deemed eligible for the Blue Badge.
Figure 1. Malicious email which contained the subject “blue badge form”
Figure 2: fraudulent login page https://www[.]verifiedbadgecenters[.]xyz/contact/
Microsoft Teams Phishing Email - Account Theft Example
In this Phishing email,
The attacker tries to lure the victim to click on the malicious link claiming that they have been added to a new team in the app. Choosing to confirm the collaboration leads to a malicious website “https://u31315517[.]ct[.]sendgrid[.]net/ls/click” which is no longer active.
Figure 3: The malicious email which contained the subject “you have been added to a new team”
Adobe Phishing Email - Account Theft Example
This phishing email, which uses Abode’s branding, was sent from the address “grupovesica@adobe-partner[.]com”, and its subject, originally in Spanish, read - “Activate your license! Take advantage of its benefits” (originally: “¡Activa tu licencia! Aprovecha sus beneficios”). In the email the victim is encouraged to contact experts to help utilize the application license.
Clicking the link in the email (“https://adobeconciergeservices[.]com/_elink/bfgkw374wekci/bcplw9h143poj/bdpip0zrm95o3”), opens a new draft message in Outlook addressed to a foreign email (not associated to Adobe), in which the user is asked to insert credit details and information for the “activation” of the license.
Figure 4: Adobe phishing email with the subject “Activate your license! Take advantage of its benefits”
Blog: https://research.checkpoint.com/
About Check Point Research
About Check Point Software Technologies Ltd.
| MEDIA CONTACT: | INVESTOR CONTACT: |
| Emilie Beneitez Lefebvre | |
| Check Point Software Technologies | |
| press@checkpoint.com | ir@us.checkpoint.com |
Photos accompanying this announcement are available at
https://www.globenewswire.com/NewsRoom/AttachmentNg/8d2e97f4-49fc-4989-9b6b-0e5232fde25e
https://www.globenewswire.com/NewsRoom/AttachmentNg/60fd68d5-0184-47ee-a4a3-c7fe18acea50
https://www.globenewswire.com/NewsRoom/AttachmentNg/5d6cdb2e-03ae-402a-83eb-f76b48235e8b
https://www.globenewswire.com/NewsRoom/AttachmentNg/7c860341-032a-42a9-8900-b8dd7f1a2bc9

![]()
Figure 1
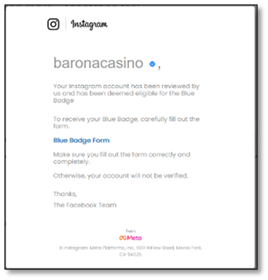
Malicious email which contained the subject “blue badge form”
Figure 2
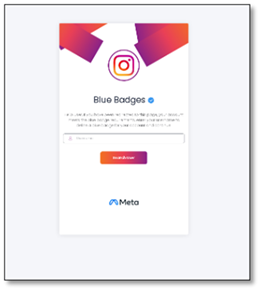
fraudulent login page https://www[.]verifiedbadgecenters[.]xyz/contact/
Figure 3
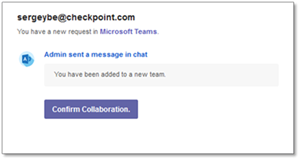
The malicious email which contained the subject “you have been added to a new team”
Figure 4

Adobe phishing email with the subject “Activate your license! Take advantage of its benefits”
2023 GlobeNewswire, Inc., source


